API Scope Management: The Complete Guide for API Platform Teams
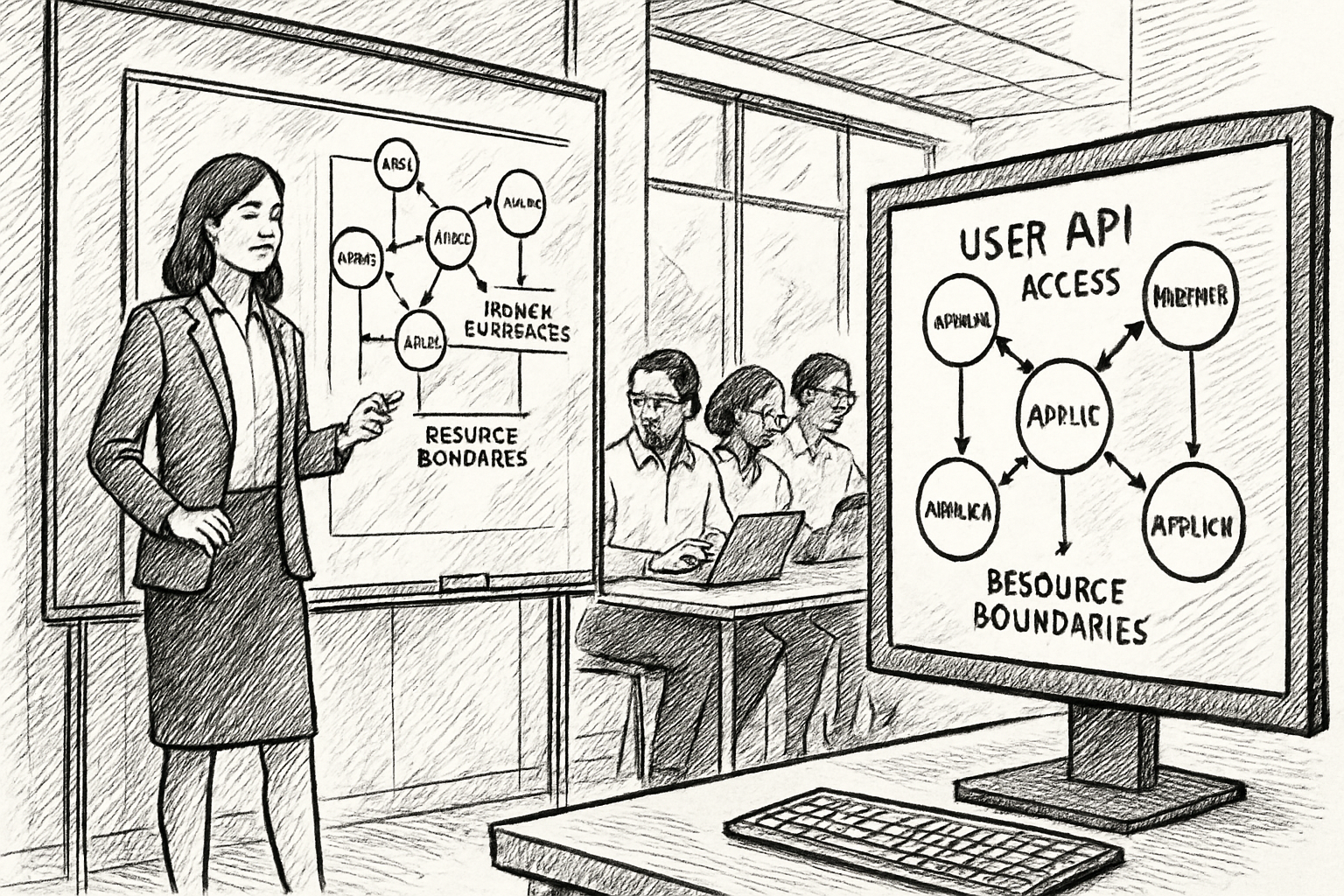
API scopes are the mechanism that controls what third-party applications can do with your APIs. They define the boundaries: which resources an application can access, what operations it can perform, and what data it can see.
Every API program that uses OAuth 2.0 has scopes. But most API programs don't manage them. Scopes get defined during development, assigned during onboarding, and then forgotten. They accumulate. They drift. And eventually, they become the gap that auditors find or the vulnerability that an incident exposes.
This guide covers everything API platform teams need to know about scope management: how scopes work, how to design them, how to enforce them, and how to manage them across the lifecycle of your partner program.
What Are API Scopes?
An API scope is a permission boundary. It defines a specific level of access that an application can request and that your authorization server can grant or deny.
In OAuth 2.0, scopes are strings included in authorization requests and access tokens. When an application requests an access token, it specifies which scopes it needs. Your authorization server decides whether to grant those scopes based on your policies. The resulting token is bound to the approved scopes, and your API enforces those boundaries on every request.
A simple example: an application with the scope read:orders can retrieve order data but can't create, update, or delete orders. An application with write:orders can create orders but can't access customer profiles. The scopes define what's possible. Your API enforces what's allowed.
Why Scope Management Matters
Scopes are easy to create and assign. They're hard to manage over time. And the gap between "we have scopes" and "we manage scopes" is where three categories of problems emerge.
Security
An over-scoped application has access to data and operations it doesn't need. If that application is compromised, the blast radius includes everything the scope grants allow, not just what the application actually uses. Scope management is the practice of keeping access aligned with need, so that compromised credentials expose the minimum possible surface area.
Compliance
Regulatory frameworks increasingly require granular access control and auditable scope grants. In healthcare, SMART on FHIR mandates resource-level scopes for patient data access. In open banking, scopes define which financial data third parties can access. In both cases, regulators expect you to prove that each application only has access to what it needs, that scope grants were approved through a governed process, and that scope management isn't manual and ad-hoc.
Operational clarity
When scopes are well-designed and consistently managed, your team can answer basic questions: What can Application X access? Why does it have that access? When was it granted? Who approved it? When scopes are unmanaged, the answers to these questions live in email threads, spreadsheets, and one person's memory.
How to Design API Scopes
Scope design is a trade-off between granularity and usability. Too few scopes and you can't enforce meaningful boundaries. Too many scopes and every authorization request becomes a negotiation.
Start with resources and operations
The most common pattern maps scopes to your API's resources and the operations available on them. If your API has orders, customers, and products, your scope structure might look like:
read:orders/write:ordersread:customers/write:customersread:products/write:products
This gives you six scopes that cover the core access patterns. An application that only needs to display order history requests read:orders. An application that creates orders on behalf of a customer requests read:orders and write:orders. An admin tool that manages everything requests all six.
In healthcare, the SMART on FHIR framework formalizes this pattern as context/ResourceType.permission. The concept is the same: scope design follows the shape of your data model.
Add context when access depends on who's asking
Sometimes the same data requires different access patterns depending on the context. A patient-facing app should only see one patient's data. A backend service might need to access data across all patients for reporting.
SMART on FHIR handles this with scope contexts: patient/Observation.read (one patient's data, authorized by that patient) vs. system/Observation.read (all observation data, authorized by the system administrator). Even outside healthcare, this pattern is useful. Consider whether your scopes need to distinguish between "access to my own data" and "access to all data."
Avoid wildcard scopes in production
A scope like * or admin:all grants unrestricted access. It's useful during development and testing. In production, it's a security and compliance risk. Every application should have the minimum scopes it needs to function. If an application needs broad access, list the specific scopes rather than granting a wildcard. The extra effort during setup pays for itself when an auditor asks what the application can access.
Design for the lifecycle, not just the launch
Scopes aren't static. Your API will evolve. New resources will be added. Existing resources will be expanded. When you add a new resource type, you'll need new scopes. When you deprecate a resource, you'll need to retire the associated scopes.
Design your scope naming convention so that new scopes are predictable. If existing scopes follow read:resource / write:resource, a new resource's scopes should follow the same pattern. Consistency in naming makes it easier for partner developers to understand what's available and for your team to manage the full scope set.
How to Enforce Scopes
Designing scopes is only half the problem. Enforcing them is the other half, and it's where most API programs have gaps.
Enforce at the authorization server
Your authorization server is the first enforcement point. When an application requests scopes, the server should validate the request against your policies:
- Is the application registered to request these scopes?
- Has the scope grant been approved (if approval is required)?
- Are the requested scopes within the set allowed for this application's registration?
If the request passes, the server issues a token bound to those scopes. If it doesn't, the server rejects the request or downgrades to the allowed subset.
Enforce at the API gateway
The API gateway is the second enforcement point. When the application presents its token to call your API, the gateway should verify that the token's scopes match the endpoint being called. A token with read:orders should be able to call GET /orders but should be rejected for POST /orders or GET /customers.
This enforcement is the runtime safety net. Even if scopes were misconfigured or over-granted, the gateway prevents access to endpoints the token doesn't cover.
Enforce at the application layer
For APIs where the same endpoint returns different data depending on the scope (for example, a user profile endpoint that returns different fields based on access level), enforcement needs to happen in the application layer. The gateway can check whether the token is valid for the endpoint. The application checks whether the specific data being returned is within the scope's boundaries.
Three layers of enforcement (authorization server, gateway, application) create defense in depth. A failure at one layer is caught by the next.
Scope Lifecycle Management
Scopes aren't a one-time setup. They have a lifecycle that runs parallel to your API's lifecycle and your partner program's growth.
Registration: capture scope requirements upfront
When a third-party application registers with your API program, it should declare which scopes it needs and why. This declaration becomes the baseline for what the application is authorized to access. If you use Dynamic Client Registration, scope requirements are captured programmatically as part of the registration request. If registration is manual, capture the scope requirements in a structured form, not in an email thread.
Approval: review before granting
Not every scope request should be auto-approved. Low-risk scopes (read-only access to non-sensitive data) might be granted automatically. High-risk scopes (write access, access to sensitive data like health records or financial information) should route through an approval workflow.
The approval should be recorded: who approved it, when, which scopes were granted, and the justification. This record is what auditors ask for. If the approval happened in Slack, you don't have a record. If it happened in an approval workflow with timestamps and approver identities, you do.
Monitoring: track what's being used
After scopes are granted, monitor whether they're actually being used. An application granted five scopes but only using two has three scopes it doesn't need. Those unused scopes are unnecessary attack surface and a compliance question waiting to be asked.
Usage monitoring doesn't need to be real-time. A monthly review that compares granted scopes against actual API usage is enough to identify over-scoped applications.
Review: validate periodically
Scope grants should be reviewed on a regular cadence. Quarterly is a reasonable starting point. For each active application, ask:
- Is the application still active?
- Is the developer organization still under a valid agreement?
- Are the granted scopes still appropriate for the application's current use case?
- Have any scopes been deprecated or replaced?
Applications that fail any of these checks should have their access adjusted or revoked.
Revocation: make it immediate
When access needs to be revoked, it needs to happen immediately. Not at the end of the billing cycle. Not when someone processes the ticket. The application's tokens should be invalidated and its scope grants removed. And the revocation should be logged with the same rigor as the original grant.
Scope Management at Scale
Everything in this guide is straightforward with five applications. It becomes a different problem with fifty, and a fundamentally different problem with hundreds.
The challenges that emerge at scale:
- Scope sprawl. As your API grows, the number of possible scope combinations grows exponentially. Without a clear naming convention and governance process, scopes multiply until nobody can explain the full set.
- Policy inconsistency. Different team members approve scopes differently. One approver grants broad access to move fast. Another requires justification for every scope. Without encoded policies, enforcement depends on who's handling the request.
- Audit burden. When an auditor asks for scope records, compiling them from multiple sources (authorization server, spreadsheets, email, Slack) takes days. At scale, you need a single system of record that can generate audit reports on demand.
- Lifecycle gaps. Applications are registered but never reviewed. Scopes are granted but never monitored. Credentials are issued but never rotated. Each gap is small. Collectively, they create the compliance risk that auditors are trained to find.
The answer to scale isn't more people doing manual work. It's tooling that encodes your policies, automates the lifecycle, and maintains the audit trail automatically.
Scope Management for Healthcare APIs
Healthcare API programs have specific scope management requirements driven by regulation.
SMART on FHIR defines a standardized scope format (context/ResourceType.permission) that all compliant implementations must support. CMS-0057-F requires scope-based access control for patient access, provider access, payer-to-payer exchange, and prior authorization APIs. ONC's HTI-1 Rule requires certified health IT to support these scopes through standardized OAuth 2.0 authorization.
For healthcare API platform teams, this means:
- Scopes must follow the SMART on FHIR format, not a custom naming convention
- Patient-level scopes must be enforced separately from system-level scopes
- Scope grants must be auditable with timestamps, approver identities, and justification
- Applications that access patient data must have scope boundaries enforced on every request
- Audit logs must capture which scopes were used for each API access event
The January 2027 compliance deadline means healthcare organizations need scope management infrastructure in place now, not when the auditor arrives.
Getting Started
If you're starting from scratch, begin with scope design. Map your API resources to scopes using the read/write:resource pattern. Keep the initial set small and expand as needed.
If you already have scopes but don't manage them, start with an audit. List every application, its granted scopes, and when those scopes were last reviewed. The gaps you find will tell you where to focus first.
If you're at scale and managing scopes manually, the priority is tooling. Encode your policies, automate approvals for low-risk scopes, build approval workflows for high-risk scopes, and create a system of record that can generate audit reports without a two-week scramble.
Apiable provides scope management as part of its API partner management platform. Application registration captures scope requirements. Approval workflows route high-risk scopes for review. Enforcement is connected to your API gateway. And the audit trail is built in. Book a demo to see how it works for your API program.